What Is Rsa Key Generation
Key generation is the process of generating keys for cryptography. The key is used to encrypt and decrypt data whatever the data is being encrypted or decrypted.
Jul 22, 2019 Universal Keygen Generator Online allows you to generate the serial numbers or product keys for all software.you can easily generate a serial key for any version and any software. It is a perfect software for beginners and professionals. It receives serial keys of recent software. It offers them genuine such as Windows 100% working Product keys. All software key generator online. Jan 19, 2020 Universal Keygen Generator Serial Key online allows you to generate the serial numbers or product keys for all software. This software has a user-friendly interface. You can easily generate a serial key for any version and any software. Nov 26, 2018 Universal Keygen Generator online allows you to generate the serial numbers or product keys for all software. This software has a user-friendly interface. This software has a user-friendly interface. You can quickly create a serial key for any version and any software. But here comes a software that helps in generation of serial keys for applications. The software in question is universal Keygen generator. Features of Universal Keygen Generator. Works with any operating system: just as the name implies, “Universal Keygen Generator”, it can function on any type of operating system. Since it can unlock program of any kind, it, therefore, works anywhere.
- May 27, 2010 H ow do I generate ssh RSA keys under Linux operating systems? You need to use the ssh-keygen command as follows to generate RSA keys (open terminal and type the following command): ssh-keygen -t rsa OR ssh-keygen Sample outputs.
- May 27, 2010 H ow do I generate ssh RSA keys under Linux operating systems? You need to use the ssh-keygen command as follows to generate RSA keys (open terminal and type the following command): ssh-keygen -t rsa OR ssh-keygen.
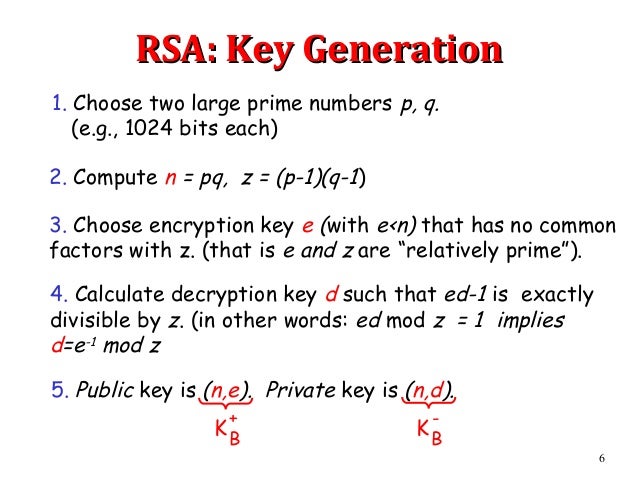
Modern cryptographic systems include symmetric-key algorithms (such as DES and AES) and public-key algorithms (such as RSA). Symmetric-key algorithms use a single shared key; keeping data secret requires keeping this key secret. Public-key algorithms use a public key and a private key. The public key is made available to anyone (often by means of a digital certificate). A sender will encrypt data with the public key; only the holder of the private key can decrypt this data.
Since public-key algorithms tend to be much slower than symmetric-key algorithms, modern systems such as TLS and its predecessor SSL as well as the SSH use a combination of the two in which:
- One party receives the other's public key, and encrypts a small piece of data (either a symmetric key or some data that will be used to generate it).
- The remainder of the conversation (the remaining party) uses a (typically faster) symmetric-key algorithm for encryption.
Jul 09, 2019 What does the Private Key look like? It looks like a block of encoded data, starting and ending with headers, such as —–BEGIN RSA PRIVATE KEY—– and —–END RSA PRIVATE KEY—–. You may not get to see this code when generating your CSR. Usually, it gets generated in the background with the CSR, and is automatically saved on your server.
The simplest method to read encrypted data is a brute force attack–simply attempting every number, up to the maximum length of the key. Therefore, it is important to use a sufficiently long key length; longer keys take exponentially longer time to attack, making a brute force attack invisible and impractical.
Currently, commonly used key lengths are:
- 128-bits for symmetric key algorithms.
- 1024-bits for public-key algorithms.
Key generation algorithms[changechange source]
In computer cryptography keys are integers. In some cases keys are randomly generated using a random number generator (RNG) or pseudorandom number generator (PRNG), the latter being a computeralgorithm that produces data which appears random under analysis. Some types the PRNGs algorithms utilize system entropy to generate a seed data, such seeds produce better results, since this makes the initial conditions of the PRNG much more difficult for an attacker to guess.
Mar 09, 2020 Microsoft Office 2013 Product Key Generator has been a part of many lives for decades. It facilitates professionals, businesses, student and individuals for personal purposes. It facilitates professionals, businesses, student and individuals for personal purposes. Jan 26, 2020 The Microsoft Office 2013 Product Key Generator is a free tool that is used to generate the activation keys for Microsoft Office 2013 for life. It must be the activation process after installing Microsoft Office 2013, but don’t worry, there is a tremendous tool that is used for the activation of Microsoft Products. 2013 standard deduction. What is the Microsoft Office 2013 Product Key? Microsoft Office 2013 product key is a 25-digit code that’s required to activate a copy of MS Office 2013. The product license key code looks like this: XXXXX-XXXXX-XXXXX-XXXXX-XXXXX. If you don’t provide a working key product code, you will not be able to use Microsoft Office 2013.
In other situations, the key is created using a passphrase and a key generation algorithm, using a cryptographic hash function such as SHA-1.
Related pages[changechange source]

- Distributed key generation: For some protocols no party should be in the sole possession of the secret key. Rather, during distributed key generation every party obtains a share of the key. A threshold of the participating parties need to work together in order to achieve a cryptographic task, such as decrypting a message.