Ubuntu Generate Rsa 2048 Key
SSH stands for “Secure Shell” and is an encrypted protocol used to log in and manage a remote server. SSH also supports various authentication mechanisms. SSH uses password-based authentication and public key-based authentication for a secure connection between a client and a server. SSH key-based authentication is more secure than password-based authentication because keys are very hard to guess or crack using currently available computing power.
In this tutorial, we will show you how to set up SSH key-based authentication on an Ubuntu 18.04 server.
Prerequisites
Apr 12, 2018 By default ssh-keygen will create a 2048-bit RSA key pair, which is secure enough for most use cases (you may optionally pass in the -b 4096 flag to create a larger 4096-bit key). After entering the command, you should see the following output. Canonical has access to the Microsoft signing PKCS#7 file (PCA 2010) (cdboot.pkcs) and its characteristics are being mimicked during key generation.Initial setup. May 05, 2019 1st create the keys and RSA will create public and private keys. If you no need add passphrase on your key then you can add passphrase with key but I skipped the passphrase on server. Is there a way to recover private key from a certificate signing request? Ask Question Asked 3 years, 6 months ago. Openssl req -new -newkey rsa:2048 -nodes -keyout yourdomain.key -out yourdomain.csr – Tristos Sep 14 '16 at. Most instructions for generating a CSR involve generating a private key and a CSR that is based on the private. Generation of primes is performed using the -G option. The desired length of the primes may be specified by the -b option. For example: # ssh-keygen -G moduli-2048.candidates -b 2048 By default, the search for primes begins at a random point in the desired length range. This may be overridden using the -S option. Step 1: Create a RSA Private Key. When creating a self-signed certificates, you must first create a server private key This key should stay private and stored on the server and not shared externally The private key is used to then create a public certificate that you can share with others To create a private key, run the commands below.
- Two fresh Ubuntu 18.04 VPS on the Atlantic.Net Cloud Platform.
- Root passwords configured on both servers.
Step 1 – Create an Atlantic.Net Cloud Server
First, log in to your Atlantic.Net Cloud Server. Create a new server, choosing Ubuntu 18.04 as the operating system with at least 2GB RAM. Connect to your Cloud Server via SSH and log in using the credentials highlighted at the top of the page.
Once you are logged into your Ubuntu 18.04 server, run the following command to update your base system with the latest available packages.
Step 2 – Generate the SSH Key on the Client Machine
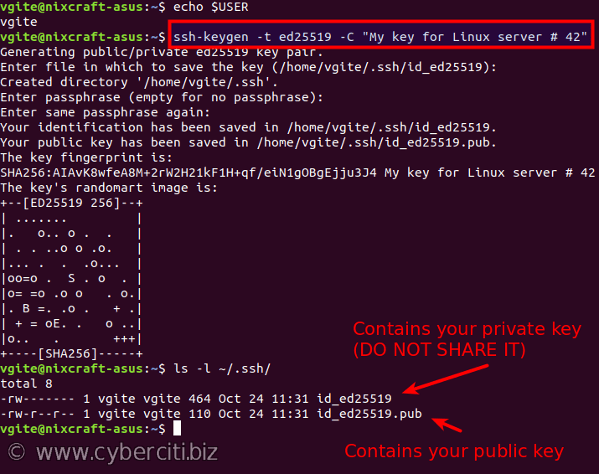
First, log in to your client machine and generate a new SSH key pair by running the following command:
You will need to press Enter to accept the default file location and provide a passphrase to add an extra layer of security, as shown below:
The above command will generate a 2048-bit RSA key pair with a secure passphrase to prevent unauthorized users from logging in.
You can see the generated public and private keys with the following command:
You should see the following output:
At this point, you have public and private keys that you can use to authenticate with your Ubuntu server.
Step 3 – Copy the Public Key to the Ubuntu Server
Next, you will need to copy the public key from the client machine to your Ubuntu 18.04 server. You can copy the public key with ssh-copy-id utility as shown below:
You should see the following output:
Type “yes” and press ENTER to continue. You should see the following output:
Next, you will be prompted to enter the remote username and password. After the successful authentication, the content of the public key ~/.ssh/id_rsa.pub will be appended to the remote user ~/.ssh/authorized_keys file as shown below:
Step 4 – Disable SSH Password Authentication
Next, log in to your Ubuntu 18.04 server machine and disable SSH password-based authentication to add an extra layer of security to your server.
You can disable password-based authentication by editing the file /etc/ssh/sshd_config:
Find the following lines and change the value to “no”:
Save and close the file, then restart SSH service to apply the configuration:
Step 5 – Log in to the Server using SSH Keys
At this point, SSH key-based authentication is configured. Now it’s time to log in to the Ubuntu 18.04 server machine with the public key.
You can login to your Ubuntu 18.04 server by simply running the following command:
If you are logging in for the first time, you will be prompted as shown below:

Type Yes and hit Enter key to continue. Next, you will be prompted to enter the passphrase for your private key as shown below:
Provide your private key passphrase and hit Enter to log in to your server.
Conclusion
In the above tutorial, we learned how to set up an SSH key-based authentication with a passphrase on Ubuntu 18.04. The connection between your client machine and Ubuntu 18.04 server machine is now highly secure. You can also use the same key for another remote server. If you’re ready to get started with SSH key-based authentication, try VPS hosting with Atlantic.Net today.
Related
Introduction
TLS, or transport layer security, and its predecessor SSL, which stands for secure sockets layer, are web protocols used to wrap normal traffic in a protected, encrypted wrapper.
Using this technology, servers can send traffic safely between the server and the client without the concern that the messages will be intercepted and read by an outside party. The certificate system also assists users in verifying the identity of the sites that they are connecting with.
In this guide, we will show you how to set up a self-signed SSL certificate for use with an Nginx web server on an Ubuntu 14.04 server. A self-signed certificate will not validate the identity of your server for your users since it is not signed by one of their web browser’s trusted certificate authorities, but it will allow you to encrypt communications with your web clients.
Note: You may want to consider using Let’s Encrypt instead of a self-signed certificate. Let’s Encrypt is a new certificate authority that issues free SSL/TLS certificates that are trusted in most web browsers. Check out the tutorial to get started: How To Secure Nginx with Let’s Encrypt on Ubuntu 14.04
Prerequisites
To get started on this guide, you will need to set up some basic things on your server.
You should have a non-root user available who has sudo privileges. You can learn how to set up such a user account by following steps 1-4 in our initial server setup for Ubuntu 14.04.
After that, you’ll also need to have the Nginx web server installed. If you would like to install an entire LEMP (Linux, Nginx, MySQL, PHP) stack on your server, you can follow our guide on setting up LEMP on Ubuntu 14.04.
If you just want the Nginx web server, you can instead just type:
Step One — Create the SSL Certificate
We can start off by creating a directory that will be used to hold all of our SSL information. Where key will be generated. We should create this under the Nginx configuration directory:
Now that we have a location to place our files, we can create the SSL key and certificate files in one motion by typing:
You will be asked a series of questions. Before we go over that, let’s take a look at what is happening in the command we are issuing:
- openssl: This is the basic command line tool for creating and managing OpenSSL certificates, keys, and other files.
- req: This subcommand specifies that we want to use X.509 certificate signing request (CSR) management. The “X.509” is a public key infrastructure standard that SSL and TLS adheres to for its key and certificate management. We want to create a new X.509 cert, so we are using this subcommand.
- -x509: This further modifies the previous subcommand by telling the utility that we want to make a self-signed certificate instead of generating a certificate signing request, as would normally happen.
- -nodes: This tells OpenSSL to skip the option to secure our certificate with a passphrase. We need Nginx to be able to read the file, without user intervention, when the server starts up. A passphrase would prevent this from happening because we would have to enter it after every restart.
- -days 365: This option sets the length of time that the certificate will be considered valid. We set it for one year here.
- -newkey rsa:2048: This specifies that we want to generate a new certificate and a new key at the same time. We did not create the key that is required to sign the certificate in a previous step, so we need to create it along with the certificate. The
rsa:2048portion tells it to make an RSA key that is 2048 bits long. - -keyout: This line tells OpenSSL where to place the generated private key file that we are creating.
- -out: This tells OpenSSL where to place the certificate that we are creating.
As we stated above, these options will create both a key file and a certificate. We will be asked a few questions about our server in order to embed the information correctly in the certificate.
Fill out the prompts appropriately. The most important line is the one that requests the Common Name (e.g. server FQDN or YOUR name). You need to enter the domain name that you want to be associated with your server. You can enter the public IP address instead if you do not have a domain name.
The entirety of the prompts will look something like this:
Both of the files you created will be placed in the /etc/nginx/ssl directory.
Step Two — Configure Nginx to Use SSL
We have created our key and certificate files under the Nginx configuration directory. Now we just need to modify our Nginx configuration to take advantage of these by adjusting our server block files. You can learn more about Nginx server blocks in this article.
Nginx versions 0.7.14 and above (Ubuntu 14.04 ships with version 1.4.6) can enable SSL within the same server block as regular HTTP traffic. This allows us to configure access to the same site in a much more succinct manner.
Your server block may look something like this:
The only thing we would need to do to get SSL working on this same server block, while still allowing regular HTTP connections, is add a these lines:
When you are finished, save and close the file.
Now, all you have to do is restart Nginx to use your new settings:
This should reload your site configuration, now allowing it to respond to both HTTP and HTTPS (SSL) requests.
Step Three — Test your Setup
Your site should now have SSL functionality, but we should test it to make sure.
First, let’s test to make sure we can still access the site with using normal HTTP. In your web browser, go to your server’s domain name or IP address:
You should see your normal website. In my example, I’m just serving the default Nginx page:
Rsa 2048 Encryption
If you get this page, then your server is still handling HTTP requests correctly.
Now, we can check whether our server can use SSL to communicate. Do this by specifying the https protocol instead of the httpUnity pro license key generator. protocol.
You will likely get a warning in your web browser that looks something like this:
Generate Rsa 2048 Bit Key
This is expected. It is telling you that it cannot verify the identity of the server you are trying to connect to because it isn’t signed by a certificate authority that the browser has been configured to trust. Since we created a self-signed certificate, this makes perfect sense.
Click on “Proceed anyway”, “Continue”, or whatever similar option is available. You should see your site again:
Your browser may show the “https” crossed out in the address bar or a broken or crossed out “lock” icon. If you click on the lock icon, you can see some more information about the connection:
Rsa 2048 Key
As you can see, the issue is only that the browser cannot verify the identity of the server because it isn’t signed by a certificate authority that it is configured to trust. The middle section shows that the connection is encrypted, however, so we have achieved that goal.
Conclusion
You have configured your Nginx server to handle both HTTP and SSL requests. This will help you communicate with clients securely and avoid outside parties from being able to read your traffic.
Ubuntu Generate Rsa 2048 Keyboard
If you are planning on using SSL for a public website, you should probably purchase an SSL certificate from a trusted certificate authority to prevent the scary warnings from being shown to each of your visitors.