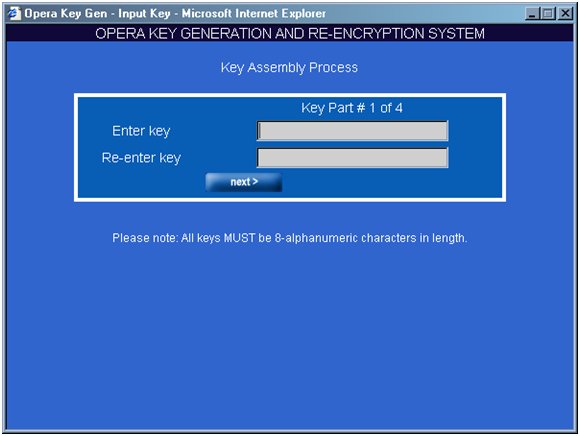
Generate Encryption Keys For The Card Data
Finally, gpg2 generates random data to make your key as unique as possible. Move your mouse, type random keys, or perform other tasks on the system during this step to speed up the process. Move your mouse, type random keys, or perform other tasks on the system during this step to speed up the process. However, you must have continuous date coverage or you will not be able to process credit cards during the dates that have no assigned encryption key; Enter the end date for this encryption; Click Generate Key button to have the system generate a unique encryption code. Click Save; Click Close; Once you have created a new encryption key, you must re-encrypt historic data with the new key and delete the old.
The encryption key server uses both symmetric and asymmetric keys; symmetric encryption for high-speed encryption of user or host data, and asymmetric encryption (which is necessarily slower) for protecting the symmetric key. Encryption keys can be generated by the encryption key server, by applications such as Tivoli Storage Manager, or by a. Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret. Microsoft generates a Key Encryption Key using the user's password. This KEK is then used to encrypt what they call the Master Key. This KEK is then used to encrypt what they call the Master Key. The Master Key is really a Data Encryption Key. Understanding Key Serial Numbers (KSN) in Derived Unique Key Per Transaction (DUKPT). Browse other questions tagged encryption cryptography des or ask your own question. Sharing Derived Unique Key Per Transaction (DUKPT) Base Derivation Key (BDK) with a partner. Use this key to enable your field level encryption implementations. Salt keys use a hex value longer than 8 bits. The encryption uses random bits with a password or passphrase to generate JWTs for custom Journey Builder activities. SSH keys allow SFTP authentication and also require an uploaded certificate.
-->Applies to
- Windows 10
How can I authenticate or unlock my removable data drive?
You can unlock removable data drives by using a password, a smart card, or you can configure a SID protector to unlock a drive by using your domain credentials. After you've started encryption, the drive can also be automatically unlocked on a specific computer for a specific user account. System administrators can configure which options are available for users, as well as password complexity and minimum length requirements. To unlock by using a SID protector, use Manage-bde:
Manage-bde -protectors -add e: -sid domainusername
What is the difference between a recovery password, recovery key, PIN, enhanced PIN, and startup key?
For tables that list and describe elements such as a recovery password, recovery key, and PIN, see BitLocker key protectors and BitLocker authentication methods.
How can the recovery password and recovery key be stored?
The recovery password and recovery key for an operating system drive or a fixed data drive can be saved to a folder, saved to one or more USB devices, saved to your Microsoft Account, or printed.
For removable data drives, the recovery password and recovery key can be saved to a folder, saved to your Microsoft Account, or printed. By default, you cannot store a recovery key for a removable drive on a removable drive.
A domain administrator can additionally configure Group Policy to automatically generate recovery passwords and store them in Active Directory Domain Services (AD DS) for any BitLocker-protected drive.
Is it possible to add an additional method of authentication without decrypting the drive if I only have the TPM authentication method enabled?
You can use the Manage-bde.exe command-line tool to replace your TPM-only authentication mode with a multifactor authentication mode. For example, if BitLocker is enabled with TPM authentication only and you want to add PIN authentication, use the following commands from an elevated command prompt, replacing 4-20 digit numeric PIN with the numeric PIN you want to use:
manage-bde –protectors –delete %systemdrive% -type tpm
manage-bde –protectors –add %systemdrive% -tpmandpin 4-20 digit numeric PIN
When should an additional method of authentication be considered?
New hardware that meets Windows Hardware Compatibility Program requirements make a PIN less critical as a mitigation, and having a TPM-only protector is likely sufficient when combined with policies like device lockout. For example, Surface Pro and Surface Book do not have external DMA ports to attack.For older hardware, where a PIN may be needed, it’s recommended to enable enhanced PINs that allow non-numeric characters such as letters and punctuation marks, and to set the PIN length based on your risk tolerance and the hardware anti-hammering capabilities available to the TPMs in your computers.
If I lose my recovery information, will the BitLocker-protected data be unrecoverable?
BitLocker is designed to make the encrypted drive unrecoverable without the required authentication. When in recovery mode, the user needs the recovery password or recovery key to unlock the encrypted drive.
Important
Store the recovery information in AD DS, along with your Microsoft Account, or another safe location.
Can the USB flash drive that is used as the startup key also be used to store the recovery key?
While this is technically possible, it is not a best practice to use one USB flash drive to store both keys. If the USB flash drive that contains your startup key is lost or stolen, you also lose access to your recovery key. In addition, inserting this key would cause your computer to automatically boot from the recovery key even if TPM-measured files have changed, which circumvents the TPM's system integrity check.
Can I save the startup key on multiple USB flash drives?
Yes, you can save a computer's startup key on multiple USB flash drives. Right-clicking a BitLocker-protected drive and selecting Manage BitLocker will provide you the options to duplicate the recovery keys as needed.
Can I save multiple (different) startup keys on the same USB flash drive?
Yes, you can save BitLocker startup keys for different computers on the same USB flash drive.
Can I generate multiple (different) startup keys for the same computer?
You can generate different startup keys for the same computer through scripting. However, for computers that have a TPM, creating different startup keys prevents BitLocker from using the TPM's system integrity check.
KEY FEATURES: Over 75 hours of story content, plus Mass Effect 3’s critically acclaimed multiplayer mode. Create and customize your own character with. Mass Effect Trilogy Origin Key GLOBAL. This package includes the three games that make up one of the most important sci-fi sagas of this generation. Create and develop your own Commander Shepard throughout the 3 games and save the galaxy from a terrible fate. Mass Effect Trilogy (PC) includes Mass Effect Pinnacle Station and Bring Down the Sky. Mass effect trilogy key generator. Mass Effect 3 Serial Key Generator As Commander Shepard, rise to become the galaxy’s most elite soldier and lead an all-out war to stop an ancient and ruthless enemy: the Reapers. COMPLETE TRILOGY PACK WITH kEYGEN AND SERIAL KEYS. Mass Effect Trilogy details Over 75 hours of story content, plus Mass Effect 3 ’s multiplayer mode. Create your own character, then play through all three Mass Effect games. Your decisions have consequences on the action and affect the story's outcome.
Can I generate multiple PIN combinations?
You cannot generate multiple PIN combinations.
What encryption keys are used in BitLocker? How do they work together?
Raw data is encrypted with the full volume encryption key, which is then encrypted with the volume master key. The volume master key is in turn encrypted by one of several possible methods depending on your authentication (that is, key protectors or TPM) and recovery scenarios.
Where are the encryption keys stored?
The full volume encryption key is encrypted by the volume master key and stored in the encrypted drive. The volume master key is encrypted by the appropriate key protector and stored in the encrypted drive. If BitLocker has been suspended, the clear key that is used to encrypt the volume master key is also stored in the encrypted drive, along with the encrypted volume master key.
This storage process ensures that the volume master key is never stored unencrypted and is protected unless you disable BitLocker. The keys are also saved to two additional locations on the drive for redundancy. The keys can be read and processed by the boot manager.
Why do I have to use the function keys to enter the PIN or the 48-character recovery password?
The F1 through F10 keys are universally mapped scan codes available in the pre-boot environment on all computers and in all languages. The numeric keys 0 through 9 are not usable in the pre-boot environment on all keyboards.
When using an enhanced PIN, users should run the optional system check during the BitLocker setup process to ensure that the PIN can be entered correctly in the pre-boot environment.
How does BitLocker help prevent an attacker from discovering the PIN that unlocks my operating system drive?
It is possible that a personal identification number (PIN) can be discovered by an attacker performing a brute force attack. A brute force attack occurs when an attacker uses an automated tool to try different PIN combinations until the correct one is discovered. For BitLocker-protected computers, this type of attack, also known as a dictionary attack, requires that the attacker have physical access to the computer.
The TPM has the built-in ability to detect and react to these types of attacks. Because different manufacturers' TPMs may support different PIN and attack mitigations, contact your TPM's manufacturer to determine how your computer's TPM mitigates PIN brute force attacks.After you have determined your TPM's manufacturer, contact the manufacturer to gather the TPM's vendor-specific information. Most manufacturers use the PIN authentication failure count to exponentially increase lockout time to the PIN interface. However, each manufacturer has different policies regarding when and how the failure counter is decreased or reset.
How can I determine the manufacturer of my TPM?

You can determine your TPM manufacturer in Windows Defender Security Center > Device Security > Security processor details.
How can I evaluate a TPM's dictionary attack mitigation mechanism?
Types Of Data Encryption
The following questions can assist you when asking a TPM manufacturer about the design of a dictionary attack mitigation mechanism:
- How many failed authorization attempts can occur before lockout?
- What is the algorithm for determining the duration of a lockout based on the number of failed attempts and any other relevant parameters?
- What actions can cause the failure count and lockout duration to be decreased or reset?
Can PIN length and complexity be managed with Group Policy?
Yes and No. You can configure the minimum personal identification number (PIN) length by using the Configure minimum PIN length for startup Group Policy setting and allow the use of alphanumeric PINs by enabling the Allow enhanced PINs for startup Group Policy setting. However, you cannot require PIN complexity by Group Policy.
For more info, see BitLocker Group Policy settings.
-->Deleting and recreating encryption keys are activities that fall outside of routine encryption key maintenance. You perform these tasks in response to a specific threat to your report server, or as a last resort when you can no longer access a report server database.
Recreate the symmetric key when you believe the existing symmetric key is compromised. You can also recreate the key on a regular basis as a security best practice.
Delete existing encryption keys and unusable encrypted content when you cannot restore the symmetric key.
Recreating Encryption Keys
If you have evidence that the symmetric key is known to unauthorized users, or if your report server has been under attack and you want to reset the symmetric key as a precaution, you can recreate the symmetric key. When you recreate the symmetric key, all encrypted values will be re-encrypted using the new value. If you are running multiple report servers in a scale-out deployment, all copies of the symmetric key will be updated to the new value. The report server uses the public keys available to it to update the symmetric key for each server in the deployment.
You can only recreate the symmetric key when the report server is in a working state. Recreating the encryption keys and re-encrypting content disrupts server operations. You must take the server offline while re-encryption is underway. There should be no requests made to the report server during re-encryption.
You can use the Reporting Services Configuration tool or the rskeymgmt utility to reset the symmetric key and encrypted data. For more information about how the symmetric key is created, see Initialize a Report Server (SSRS Configuration Manager).
How to recreate encryption keys (Reporting Services Configuration Tool)
Disable the Report Server Web service and HTTP access by modifying the IsWebServiceEnabled property in the rsreportserver.config file. This step temporarily stops authentication requests from being sent to the report server without completely shutting down the server. You must have minimal service so that you can recreate the keys.
If you are recreating encryption keys for a report server scale-out deployment, disable this property on all instances in the deployment.
Open Windows Explorer and navigate to drive:Program FilesMicrosoft SQL Serverreport_server_instanceReporting Services. Replace drive with your drive letter and report_server_instance with the folder name that corresponds to the report server instance for which you want to disable the Web service and HTTP access. For example, C:Program FilesMicrosoft SQL ServerMSRS10_50.MSSQLSERVERReporting Services.
Open the rsreportserver.config file.
For the IsWebServiceEnabled property, specify False, and then save your changes.
Start the Reporting Services Configuration tool, and then connect to the report server instance you want to configure.
On the Encryption Keys page, click Change. Click OK.
Restart the Report Server Windows service. If you are recreating encryption keys for a scale-out deployment, restart the service on all instances.
Re-enable the Web service and HTTP access by modifying the IsWebServiceEnabled property in the rsreportserver.config file. Do this for all instances if you are working with a scale out deployment.
How to recreate encryption keys (rskeymgmt)
Disable the Report Server Web service and HTTP access. Use the instructions in the previous procedure to stop Web service operations.
Run rskeymgmt.exe locally on the computer that hosts the report server. Use the -s argument to reset the symmetric key. No other arguments are required:
Restart the Reporting Services Windows service.
Deleting Unusable Encrypted Content
If for some reason you cannot restore the encryption key, the report server will never be able to decrypt and use any data that is encrypted with that key. To return the report server to a working state, you must delete the encrypted values that are currently stored in the report server database and then manually re-specify the values you need.
Deleting the encryption keys removes all symmetric key information from the report server database and deletes any encrypted content. All unencrypted data is left intact; only encrypted content is removed. When you delete the encryption keys, the report server re-initializes itself automatically by adding a new symmetric key. The following occurs when you delete encrypted content:
Connection strings in shared data sources are deleted. Users who run reports get the error 'The ConnectionString property has not been initialized.'
Stored credentials are deleted. Reports and shared data sources are reconfigured to use prompted credentials.
Reports that are based on models (and require shared data sources configured with stored or no credentials) will not run.
Subscriptions are deactivated.
Once you delete encrypted content, you cannot recover it. You must re-specify connection strings and stored credentials, and you must activate subscriptions.
You can use the Reporting Services Configuration tool or the rskeymgmt utility to remove the values.
How to delete encryption keys (Reporting Services Configuration Tool)
Encryption Key Example
Start the Reporting Services Configuration tool, and then connect to the report server instance you want to configure.
Click Encryption Keys, and then click Delete. Click OK.
Restart the Report Server Windows service. For a scale-out deployment, do this on all report server instances.
How to delete encryption keys (rskeymmgt)
Run rskeymgmt.exe locally on the computer that hosts the report server. You must use the -d apply argument. The following example illustrates the argument you must specify:
Restart the Report Server Windows service. For a scale-out deployment, do this on all report server instances.
How to re-specify encrypted values
For each shared data source, you must retype the connection string.
For each report and shared data source that uses stored credentials, you must retype the user name and password, and then save. For more information, see Specify Credential and Connection Information for Report Data Sources.
For each data-driven subscription, open each subscription and retype the credentials to the subscription database.
For subscriptions that use encrypted data (this includes the File Share delivery extension and any third-party delivery extension that uses encryption), open each subscription and retype credentials. Subscriptions that use Report Server e-mail delivery do not use encrypted data and are unaffected by the key change.
See Also
Generate Encryption Keys For The Card Data Plan
Configure and Manage Encryption Keys (SSRS Configuration Manager)
Store Encrypted Report Server Data (SSRS Configuration Manager)
