Java Rsa Key Generation Example
RSA algorithm is asymmetric cryptography algorithm. Asymmetric actually means that it works on two different keys i.e. Public Key and Private Key. As the name describes that the Public Key is given to everyone and Private key is kept private. An example of asymmetric cryptography. Apr 22, 2017 RSA algorithm is asymmetric cryptography algorithm. Asymmetric actually means that it works on two different keys i.e. Public Key and Private Key. As the name describes that the Public Key is given to everyone and Private key is kept private. An example of asymmetric cryptography. Key Generation. In lecture, we learned about RSA and how to implement RSA key generation in Java using the fields and methods of the BigInteger class. Problem 2: Write a Java method keyGenerate selects an n and calculates the values of k and d. Make two copies of your prelab code. Submit one copy to your Lab TA at the beginning of lab session. Java program to encrypt and decrypt a given message using RSA algorithm. Open Command Prompt and compile & Run. RSA algorithm is used to changing message that no one can understand the communication between sender and receiver. Sender and Receiver have public and private key and they can only understand message. JAVA Program import java.math.BigInteger;. Feb 02, 2013 Java Code for RSA Key Generation. Java Code for RSA Key Generation. Skip navigation Sign in. How SSL works tutorial - with HTTPS example. Aug 30, 2016 شرح كامل للتشفير و فك التشفير وعمل المفتاح عن طريق شيفرة rsa بطريقة مبسطة مع حل مثال. Here is an example of creating a Java KeyPairGenerator instance: KeyPairGenerator keyPairGenerator = KeyPairGenerator.getInstance('RSA'); The getInstance method takes the name of the encryption algorithm to generate the key pair for. In this example we use the name RSA. Initializing the KeyPairGenerator.
- Rsa Key Generation Example
- Java Rsa Key Generation Example Free
- Java Rsa Key Generation Example Pdf
- Java Rsa Key Generation Example 2
- Rsa Public Key Example
Contents
- 3. Saving the Keys in Binary Format
- Source Code
1. Introduction
Let us learn the basics of generating and using RSA keys in Java.
Java provides classes for the generation of RSA public and private key pairs with the package java.security. You can use RSA keys pairs in public key cryptography.
Crypto key generate rsa modulus 1024 cisco. I did a little research and found out that if I removed the rsa key by using this command ' crypto key zeroize rsa' and then added the 'crypto key generate rsa generate-keys modulus 1024, then that would work. Any thoughts? No service pad. No service password-encryption. Hostname Sales-SW-ACC2. Ip domain name my.company.come. Feb 05, 2014 crypto key generate rsa modulus 1024 on cisco 1800 series to create a Trustpoints Gustavo Jan 24, 2014 12:53 PM tengo un problema al querer configurar un tunnel con PKI. Router(config)# crypto key generate rsa label ms2 modulus 2048 on usbtoken0: The name for the keys will be: ms2% The key modulus size is 2048 bits% Generating 1024 bit RSA keys, keys will be. Oct 02, 2015 SSH Config and crypto key generate RSA command. Use this command to generate RSA key pairs for your Cisco device (such as a router). Keys are generated in pairs–one public RSA key and one private RSA key. If your router already has RSA keys when you issue this command, you will be warned and prompted to replace the existing keys with new keys.
Public key cryptography uses a pair of keys for encryption. Distribute the public key to whoever needs it but safely secure the private key.
Public key cryptography can be used in two modes:
Encryption: Only the private key can decrypt the data encrypted with the public key.
Authentication: Data encrypted with the private key can only be decrypted with the public key thus proving who the data came from.
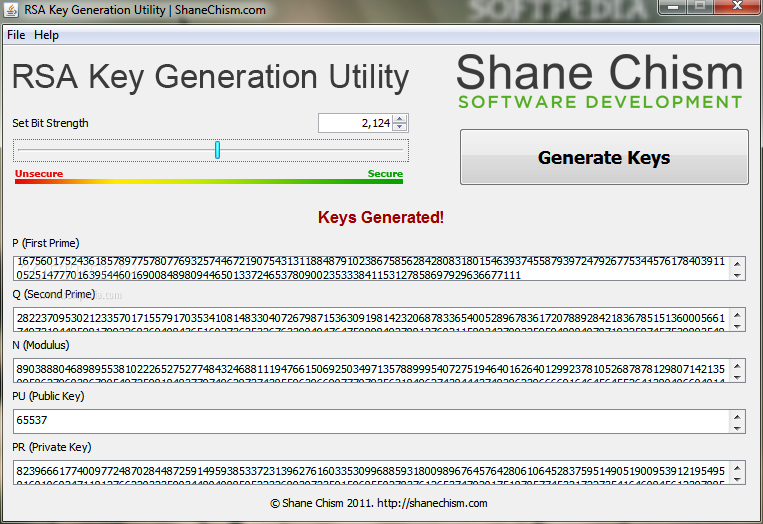
2. Generating a Key Pair
First step in creating an RSA Key Pair is to create a KeyPairGeneratorfrom a factory method by specifying the algorithm (“RSA” in this instance):
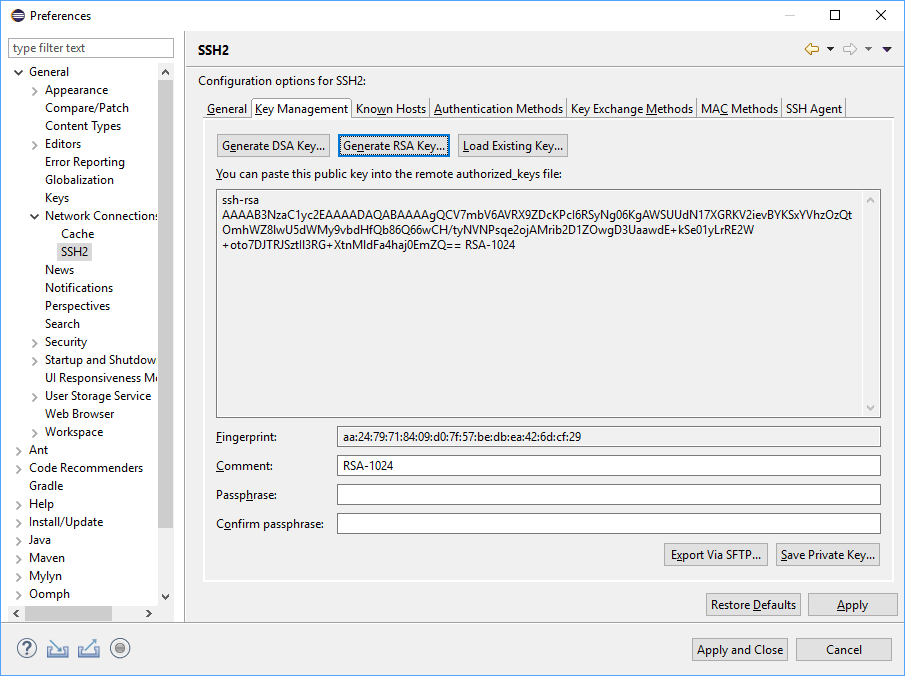
Initialize the KeyPairGenerator with the key size. Use a key size of 1024 or 2048. Currently recommended key size for SSL certificates used in e-commerce is 2048 so that is what we use here.
From the KeyPair object, get the public key using getPublic() and the private key using getPrivate().
3. Saving the Keys in Binary Format
Save the keys to hard disk once they are obtained. This allows re-using the keys for encryption, decryption and authentication.
What is the format of the saved files? The key information is encoded in different formats for different types of keys. Here is how you can find what format the key was saved in. On my machine, the private key was saved in PKCS#8 format and the public key in X.509 format. We need this information below to load the keys.
3.1. Load Private Key from File
After saving the private key to a file (or a database), you might need to load it at a later time. You can do that using the following code. Note that you need to know what format the data was saved in: PKCS#8 in our case.
Rsa Key Generation Example
3.2 Load Public Key from File
Load the public key from a file as follows. The public key has been saved in X.509 format so we use the X509EncodedKeySpec class to convert it.
4. Use Base64 for Saving Keys as Text
Java Rsa Key Generation Example Free
Save the keys in text format by encoding the data in Base64. Java 8 provides a Base64 class which can be used for the purpose. Save the private key with a comment as follows:
Mar 26, 2020 Microsoft Office 2010 product key Generator stands as one of the most popular, versatile and complete office application suites in the world, and its popularization has spread to such an extent that more than 80% of companies use the services of this software on day to day basis. Microsoft Office is a set of applications with which we can carry out office tasks, being able to automate and achieve a. Microsoft office 2010 key generator.
And the public key too (with a comment):
5. Generating a Digital Signature
As mentioned above, one of the purposes of public key cryptography is digital signature i.e. you generate a digital signature from a file contents, sign it with your private key and send the signature along with the file. The recipient can then use your public key to verify that the signature matches the file contents.
Here is how you can do it. Use the signature algorithm “SHA256withRSA” which is guaranteed to be supported on all JVMs. Use the private key (either generated or load from file as shown above) to initialize the Signatureobject for signing. It is then updated with contents from the data file and the signature is generated and written to the output file. This output file contains the digital signature and must be sent to the recipient for verification.
Java Rsa Key Generation Example Pdf
6. Verifying the Digital Signature
The recipient uses the digital signature sent with a data file to verify that the data file has not been tampered with. It requires access to the sender’s public key and can be loaded from a file if necessary as presented above.
The code below updates the Signature object with data from the data file. It then loads the signature from file and uses Signature.verify() to check if the signature is valid.
Java Rsa Key Generation Example 2
And that in a nutshell is how you can use RSA public and private keys for digital signature and verification.
Rsa Public Key Example
Source Code
Go here for the source code.